A new alert regarding a phishing attack involving Facebook Messenger appears to be on the rise. The mechanism of action was described to be stealing the app’s credentials that are used to handle Facebook’s pages. And that’s simply by impersonating the company’s support team through chatbots on the app.
Chatbots is another term reserved for programs that copy team members in an app so deceivingly that users can never know the difference if they’re talking to a live support team member or a chatbot. And then, in normal cases, the command is passed on to the real team member for further assistance.
But in this case, phishing attacks have nothing but malicious intentions. And we’re thankful to Trustwave who first highlighted the alarming news.
See, these threat actors’ main goal is to use the chatbots and take away credentials from managers leading Facebook pages. And instead of providing genuine support that helps in promoting the app’s services, the purpose is nothing but harm.
At first, users will receive an email that informs them how their page was recently violated and hence is against the app’s community guidelines. They will then be given just 2 days to generate an appeal or face the consequences which in this case is page deletion.
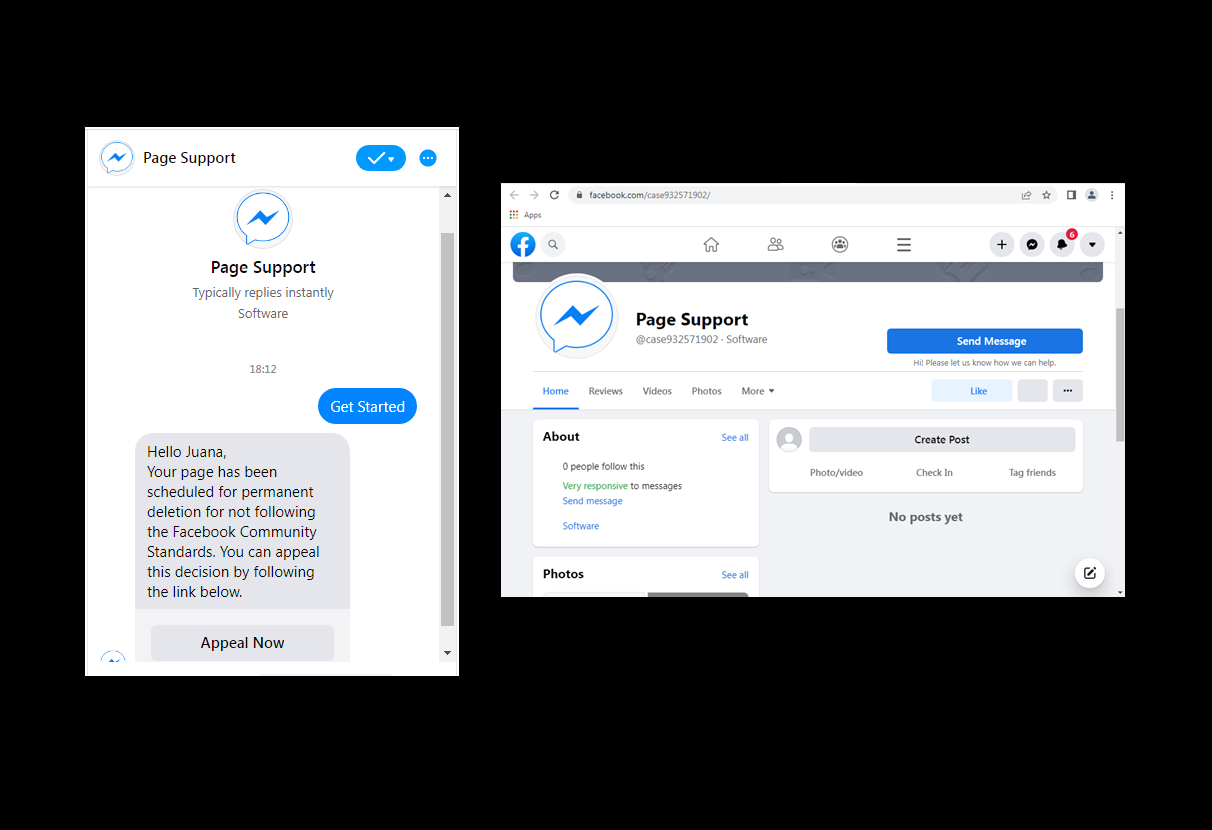
Those who wish to appeal are given a link and told to click on it that comes with the label ‘Appeal Now’. Soon, they’re transferred directly to the conversation where they’ll seek a chatbot that copies a live representative from the Facebook team. Here, if you’re smart enough to check the account, you’ll find the page linked to the chatbot really has zero followers and comes without any posts too.
In the end, users are guided to the Support Inbox on Facebook but interestingly, they won't be seeing any URL as a component of the domain on the app. In the pointers released by Trustwave, they’ve also shown how a case number will not match that presented to the viewer at an earlier stage. Still, the fraud is very hard to detect.
Next, users need to punch in their details like email, name, page name, and number. And soon after that, a password is needed and the information is sent out to a database held by the impersonator. And in the end, victims get redirected toward a new page where they add OTPs via messages, making a viewer feel the page is so authentic.
Once that is completed, users will land up at the real Facebook page that is aligned with the violation guidelines. But it’s amazing how the whole thing is so automated that you’d never be able to tell the difference.
Moreover, the real exploitation could actually end up coming at a later point in time so users find out pretty late, if ever.
So what benefit are these phishing attacks gaining? Well, other than credentials, it’s also related to bigger volume operations without much effort or time being spent. And the simple fact that AI technology is being used makes these incidents much more difficult to detect.
Experts believe the best protection against such events is double-checking URLs and never entering credentials when in doubt.
Read next: Here’s How the Cybersecurity Landscape Might Look By 2025 According Gartner’s New Report
Chatbots is another term reserved for programs that copy team members in an app so deceivingly that users can never know the difference if they’re talking to a live support team member or a chatbot. And then, in normal cases, the command is passed on to the real team member for further assistance.
But in this case, phishing attacks have nothing but malicious intentions. And we’re thankful to Trustwave who first highlighted the alarming news.
See, these threat actors’ main goal is to use the chatbots and take away credentials from managers leading Facebook pages. And instead of providing genuine support that helps in promoting the app’s services, the purpose is nothing but harm.
At first, users will receive an email that informs them how their page was recently violated and hence is against the app’s community guidelines. They will then be given just 2 days to generate an appeal or face the consequences which in this case is page deletion.
Those who wish to appeal are given a link and told to click on it that comes with the label ‘Appeal Now’. Soon, they’re transferred directly to the conversation where they’ll seek a chatbot that copies a live representative from the Facebook team. Here, if you’re smart enough to check the account, you’ll find the page linked to the chatbot really has zero followers and comes without any posts too.
In the end, users are guided to the Support Inbox on Facebook but interestingly, they won't be seeing any URL as a component of the domain on the app. In the pointers released by Trustwave, they’ve also shown how a case number will not match that presented to the viewer at an earlier stage. Still, the fraud is very hard to detect.
Next, users need to punch in their details like email, name, page name, and number. And soon after that, a password is needed and the information is sent out to a database held by the impersonator. And in the end, victims get redirected toward a new page where they add OTPs via messages, making a viewer feel the page is so authentic.
Once that is completed, users will land up at the real Facebook page that is aligned with the violation guidelines. But it’s amazing how the whole thing is so automated that you’d never be able to tell the difference.
Moreover, the real exploitation could actually end up coming at a later point in time so users find out pretty late, if ever.
So what benefit are these phishing attacks gaining? Well, other than credentials, it’s also related to bigger volume operations without much effort or time being spent. And the simple fact that AI technology is being used makes these incidents much more difficult to detect.
Experts believe the best protection against such events is double-checking URLs and never entering credentials when in doubt.
Read next: Here’s How the Cybersecurity Landscape Might Look By 2025 According Gartner’s New Report