Apple has been one of the biggest creators of smartphones for a long time now. We see that they have come up with many products like iPhone, iPod, iPad and what not. They have made sure that the products they are providing are of the highest quality and have gone through proper security checks so that they could become reliable and safe for them.
But sometimes, even the biggest of companies run into problems when they find bugs or an attack that might just threaten their integrity and credibility and that is what has happened to Apple as well.
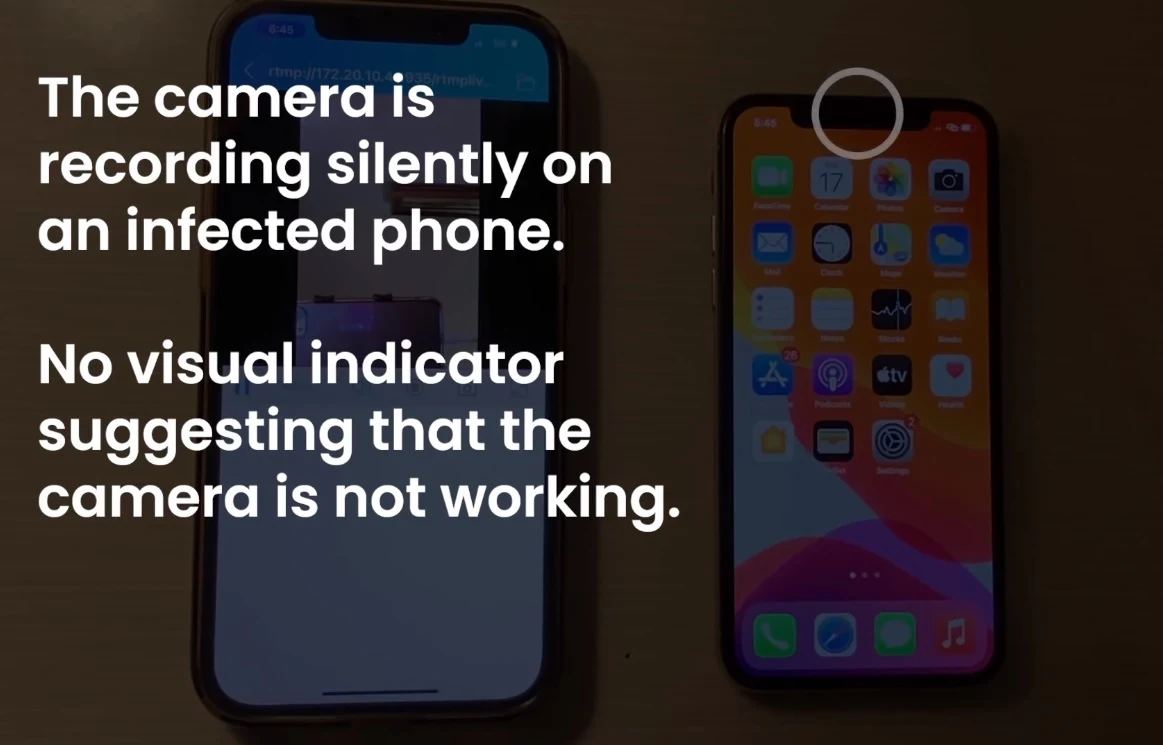
Researchers have found a new way that would fake a power off or restart the iPhone, that would prevent the phone from getting rid of all the dangerous malware that is present in the phone. This fake reboot might just give the attacker that time frame where they can access your camera and microphone that would enable them to spy on you.
Whenever an iPhone was suspected to be exposed to any threatening malware, users would just reboot the phone so that these malwares would get deleted from the memory. What happens here is that the phone never actually turns off or reboots. Instead, it allows the malware to stay in the system when the user starts the phone again.
This attack is a kind of a passive attack, which is also known as snooping where the attacker just finds access to your data and doesn’t really harm your data but he can use it whenever he wants.
They are calling this the “NoReboot” attack which means that it occurs because of the error made by the user and not the IOS thus it cannot be patched by them.
So how does this happen? Well security researchers at ZecOps came up with a Trojan PoC tool which injects a specialized code into the system of the iOS which would enable a fake reboot by disabling all the indicators. It pauses the signal that it sent to the “Spring Board” and sends a code to it that would make it exit the system forcefully, which would cause the app not to respond to any touch or commands given by the user.
Now the “BackBoardd” daemon is instructed in a way that it shows the spinning wheel sign on the screen telling the user that the phone is shutting down. This daemon also logs the power button so it can be abused if used by the Trojan correctly. When the user attempts to turn on the phone, it makes the user release the button earlier than they should because that would enable the phone to restart.
The user is now left with the normal UI with him believing that their phone has actually rebooted whereas the phone was never really turned off.
Attackers and developers can now have the upper hand by using this technique, where the old restart method fails to delete the injected malwares.
Read next: There Are Over 1,200 Online Phishing Toolkits According to This Study
But sometimes, even the biggest of companies run into problems when they find bugs or an attack that might just threaten their integrity and credibility and that is what has happened to Apple as well.
Researchers have found a new way that would fake a power off or restart the iPhone, that would prevent the phone from getting rid of all the dangerous malware that is present in the phone. This fake reboot might just give the attacker that time frame where they can access your camera and microphone that would enable them to spy on you.
Whenever an iPhone was suspected to be exposed to any threatening malware, users would just reboot the phone so that these malwares would get deleted from the memory. What happens here is that the phone never actually turns off or reboots. Instead, it allows the malware to stay in the system when the user starts the phone again.
This attack is a kind of a passive attack, which is also known as snooping where the attacker just finds access to your data and doesn’t really harm your data but he can use it whenever he wants.
They are calling this the “NoReboot” attack which means that it occurs because of the error made by the user and not the IOS thus it cannot be patched by them.
So how does this happen? Well security researchers at ZecOps came up with a Trojan PoC tool which injects a specialized code into the system of the iOS which would enable a fake reboot by disabling all the indicators. It pauses the signal that it sent to the “Spring Board” and sends a code to it that would make it exit the system forcefully, which would cause the app not to respond to any touch or commands given by the user.
Now the “BackBoardd” daemon is instructed in a way that it shows the spinning wheel sign on the screen telling the user that the phone is shutting down. This daemon also logs the power button so it can be abused if used by the Trojan correctly. When the user attempts to turn on the phone, it makes the user release the button earlier than they should because that would enable the phone to restart.
The user is now left with the normal UI with him believing that their phone has actually rebooted whereas the phone was never really turned off.
Attackers and developers can now have the upper hand by using this technique, where the old restart method fails to delete the injected malwares.
Read next: There Are Over 1,200 Online Phishing Toolkits According to This Study